Securing AI agents with AWS and Cisco AI Defense
💡Discover how to secure enterprise AI agent deployments with Cisco and AWS.
⚡ 30-Second TL;DR
What Changed
Addresses security challenges in scaling AI agents
Why It Matters
Provides enterprises with a robust framework to deploy AI agents securely, ensuring that agent-to-agent communication remains compliant and monitored.
What To Do Next
Evaluate your current AI agent governance policy against the Cisco and AWS security framework for A2A deployments.
🧠 Deep Insight
Web-grounded analysis with 19 cited sources.
🔑 Enhanced Key Takeaways
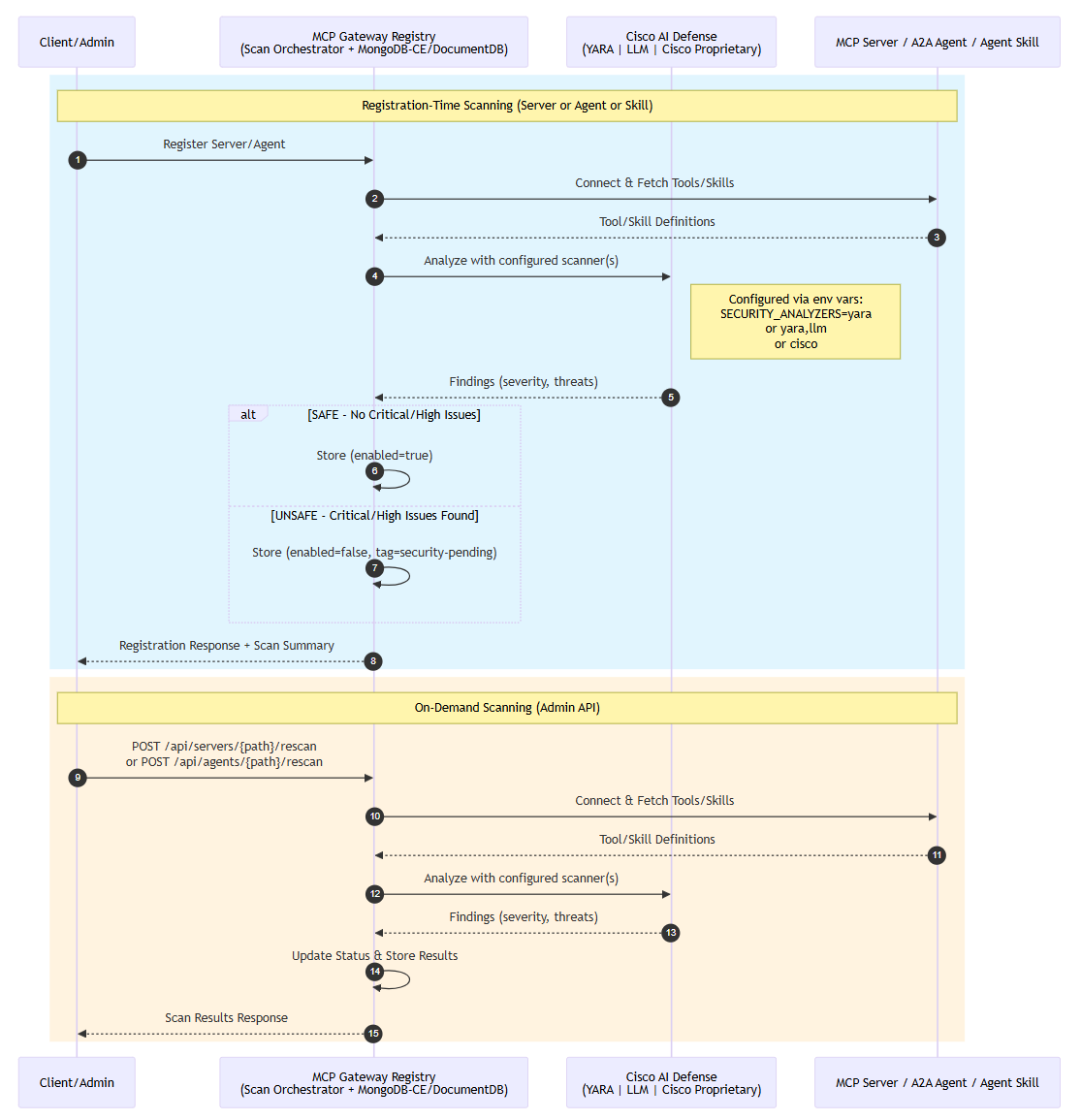
- •The joint solution provides end-to-end security across the entire AI application lifecycle, encompassing development, deployment, and runtime phases, with a focus on continuous validation and protection.
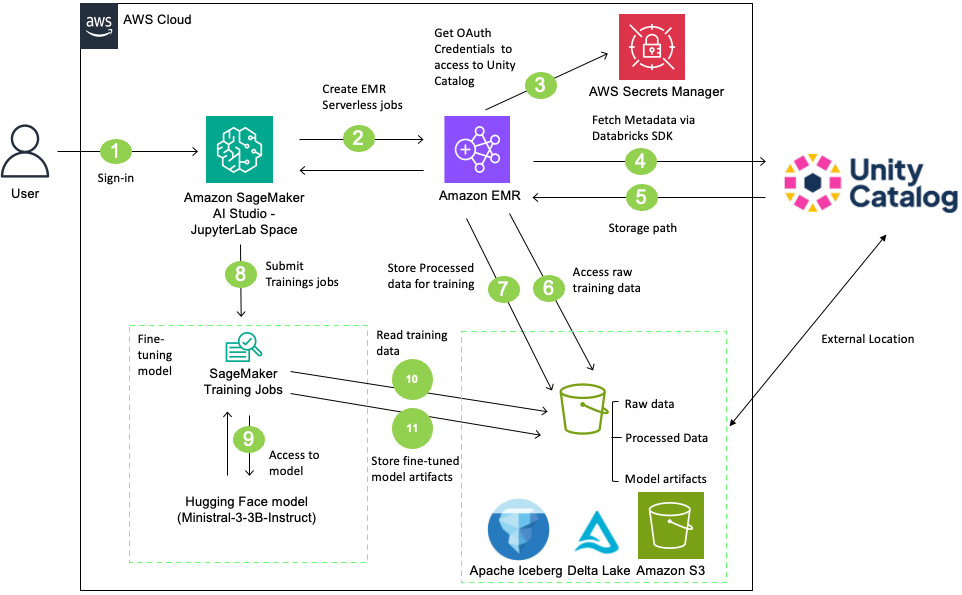
- •Cisco AI Defense integrates with core AWS AI services, including Amazon Bedrock and SageMaker, to offer automated vulnerability detection and real-time guardrails against AI-specific threats.
- •The partnership directly addresses emerging AI threats such as prompt injection, data poisoning, model manipulation, adversarial attacks, and the risks associated with 'shadow AI' applications.
- •Cisco has introduced an 'Explorer Edition' of its AI Defense solution, enabling enterprises to perform self-service red teaming and assess the risk posture of AI models and applications before they are deployed into agentic workflows.
- •AWS contributes a comprehensive security fabric for autonomous systems, utilizing services like Amazon Bedrock Guardrails, AWS Step Functions, Amazon Bedrock AgentCore, AWS IAM, and Amazon GuardDuty to build auditable and trustworthy AI agents.
📊 Competitor Analysis▸ Show
| Feature/Provider | AWS & Cisco AI Defense | Palo Alto Networks | Microsoft | SentinelOne | CyberArk |
|---|---|---|---|---|---|
| Core Focus | End-to-end AI agent security, lifecycle protection, hybrid cloud integration, MCP/A2A. | AI-driven threat detection, identity security, cloud security, security orchestration. | AI-driven threat detection, identity security, cloud security, security orchestration. | AI-driven threat detection, identity security, cloud security, security orchestration. | Identity-first approach to securing autonomous AI agents, privilege control, lifecycle management. |
| Key Capabilities | Automated vulnerability testing, runtime guardrails, network-layer visibility, compliance with NIST, OWASP, MITRE ATLAS. | AI-driven SOC platform (Cortex XSIAM) with SIEM, SOAR, XDR, NDR. | AI-driven threat detection, identity security, cloud security. | AI-driven threat detection, real-time monitoring, automated response. | AI agent discovery, context enrichment, privilege control, threat detection. |
| AI Threat Mitigation | Prompt injection, data poisoning, model manipulation, adversarial attacks, shadow AI. | Thousands of analytics models and detections, alert noise reduction. | Capabilities in AI-driven threat detection. | Real-time monitoring, automated response, protection of agent-driven environments. | Reduces risks from over-permissioned or unmanaged agents. |
| Deployment Model | Integrated with AWS cloud services, Cisco Security Cloud. | Unified SOC platform. | Cloud-based, integrates with Microsoft ecosystem. | Cloud-based. | SaaS, cloud, developer environments. |
| Compliance/Standards | Aligns with NIST, MITRE ATLAS, OWASP LLM Top 10. | - | - | - | - |
| Unique Offerings | Cisco AI Defense: Explorer Edition for self-service red teaming; AWS AgentCore Identity for secure agent access. | Cortex XSIAM consolidates multiple security capabilities. | Strong position in the agentic AI security market. | Strong position in the agentic AI security market. | Focus on AI agents as a new class of privileged identities. |
🛠️ Technical Deep Dive
🔮 Future ImplicationsAI analysis grounded in cited sources
⏳ Timeline
📎 Sources (19)
Factual claims are grounded in the sources below. Forward-looking analysis is AI-generated interpretation.
- vertexaisearch.cloud.google.com — Auziyqgpaxpen32cfqcwtdzf5 Evcwwwemuu7n5qwgra4afcghfvypg0xwsd8c4n Epn4p 2ljiejjadqgikuxm9emnbrflewaa4khtg W4 Q Eolb3d3ifbecan Qdhhf45ume Ia4e81pjzx3wco 87wruiw=
- vertexaisearch.cloud.google.com — Auziyqhdn3ntjaawx8xqqwa8bwq3pfgsugommnw9xybaj5ratxddyrcqpqp65u1e 0hbht44zgfmcmtirlvqulkom5gogzssowtcxmxgfoqqc Fa3kenu2x04uvaij8dxcw1cbs5dm3wuyog6sjatwc01wk8 F3sixfk6nnhfwlzql B5z4pruaau6lcebw5hoc 0dqz5m4=
- vertexaisearch.cloud.google.com — Auziyqehkxa7v7uppnlym9n9ow Wzltwuh388acsam8 2pjny8fts Fzbcxudzkx5mtmqbefxra5fxbqcejj2e 4iqoexzkxcbvzjumawli9ly597qyveg5tgbu P L3wuyaxbttekqwha39evte2db1m39sfdtf9830ew==
- vertexaisearch.cloud.google.com — Auziyqgbb9ad6hkzgsb5sjs7cbzyknptx 5mncj Ijuihfh8wadgnpwd8m3tt7s9iudnsdvlb7gxhrlq1qqvmivhtng3x29yg729t5o30d8wwnz Sky6fhaoatgzds5a Ehchlkdcuyqppjoubqzymsyn9pzkvwr Wd Io5a8fasj8hf4cutn1nk9ul2punljocjbfyuxq Zodzvkqkx11wygvnzciws1afj
- vertexaisearch.cloud.google.com — Auziyqgitcp Rnzypxfcbkjlymva0gsabopkg2d Bdi4jcsmmlmmqdwzj855yx Z7swtty3kzzsajkcmhrtfz0li2ul6xre9bwtdbiqialuikvd9fpndretwsi58a 7b9fguwy2jw F39ktscdj3eqgaleepke 3w9rn6ul2mp3pacavvg42y Tkrwuqtvy9evfieu43
- vertexaisearch.cloud.google.com — Auziyqf9urhfppvq5w51j 2toqfv1b10a0jmuf3kagy0a6iwxinxs Vupphb6xan Dxp0vqlyu Vewdqd Xy5pun Xtjtji Fglo2phl7pkrw5qfoe Cdvusjiicpntz0tgdiqjhmq6uvb2md Tqndcpaawhumnp3dfxjwvakk7owduare0uikbyrbpf2crbm0jfl3rjbvewltl Jpltudc=
- vertexaisearch.cloud.google.com — Auziyqf18mcwftt06 Ewnem7 I Hemtdxsq75fpnh4mbyjvh8o17 1p3cppyggfjburw Unha6opkjp9i2lm0wmmei7 Qfxqibamtwojjq4r0sk4fiodhitafmaxf4lkbydaiuloc3jqn23ah7bcv Iidizyrxa42t8pzniwtxecsyhojzkl
- vertexaisearch.cloud.google.com — Auziyqglyjpdybsiyd Ucd5v4k Cly 4566qxhofvuvzgd3c1hpl23hmtxpljxwduyvy9o8nw5dwouyiq1tumcpa6es7vjsjpgsm6pxuz5p Qlylisniuclm8ns03amnao3tuhdlxvq Rpbwo9odfuju31sixjcawzjcybbdyvvckpmvgeiwz5t 0dndd5jdmxxmmo0d8pahza4otw5kcugiickn1a==
- vertexaisearch.cloud.google.com — Auziyqgvnma2kppjwvslgate4jeenrnc7hcwx08top Banhqnztelspebutuvxabdxxrhle3km6n036em8qdwbpyonpqaekurxteach3chs8uij2 Aaro7xtijmh3alh2o0fdthbej23hjpaqxbk5acfffnv4ukidjuapxw3uszzcikaleod6q==
- vertexaisearch.cloud.google.com — Auziyqglkt95w Vesid Kcb8ougcu1t Rllci02o Ajj2syal1tsrejf43oat9005dfuj3n8158zlesoi Kl83c0mh14dubnrfyp3dhvkmofdoh2biikya5fvk5ocucgut6dsjj1nrmijnfhkktmx71azzjw6qqlce4pvj2khyp5o Tj3lmyvfba8xry5n9srvr
- vertexaisearch.cloud.google.com — Auziyqerrwwjphzurcvgetfxrcvnow2nm4yjrx3fdt0g6qxehk1mi28bnujvvdmq6dvymxqpgpnf2eo6qg5sycbchr5op9sn Hnhdgl6nn8odyutcxiiwzxpok5jjxzwjael4cmnmgxm8gpr5ughsmm0mg20vxtpisckddd Ityh7onua6jnivn84hp1 Pdzjgo=
- vertexaisearch.cloud.google.com — Auziyqhm88k4klukk0lxzvvoun8b1gx7lzjofqplmt4axdmyreu6ggvvouhhaq8ibsnj86nxzwu Ll1gmz2cyelkjfu F67zrh39imcxw1bfy3llalksgyzkqtu6c Cvkhi3wutr8ewpw2g3zbyiqualwl1bb6xwdva49murcsghtbyy2skn06ly12atrtbq A==
- vertexaisearch.cloud.google.com — Auziyqeesqrw875vmvmu9h25pmzw2kjaxta2cf0f Y5 Alsuvl4ye Cjjzjdwq0zw76uge0v5yglqrovpix9 Sdhukx7ueboofsakb7 Ocugz7nmzhzowspr5hgyriv4ixgpzv3dabiw 8epv8fznmmxtrq6fznabdjofmhsmpbryxtql0ndvt7gvtvbiskiims=
- vertexaisearch.cloud.google.com — Auziyqffgfc2avor8oxzo02bgzfj3ibuxfg8j4vqicrwop00xajtnnw5m Yuogero Yrbjkyvjew8c6gx1hasychpagvapthizdbfcr2ykt1pc2vvte2fol6xjfsttjlvhq2qlpoumewhuoxtv9r8vbslmx8o7zzj Veqz1ikj1vjz0p 87lf1guhtfy D Jh8tny0ctgzth02d4mfyexp Djfrgkceicl5y B6xrfv2bb0h
- vertexaisearch.cloud.google.com — Auziyqg37fw3ezyfqm Ypc7mts6dynplrnxwhvczpza71gry8gkcus Pxqxbj3 Fyfk Kqvyfeoeudk2yizhqxnrgxe Zzjuq7vevacbrfp1h80v4tfys0q2eodqsqczsfi7m V05y1kbxwhwvajt An2iulxtkd06jfc3d6fdj2mbsburkpjkrlmnzyoay9lv5zzlgprdbwk5it87kbskyv Fgrvidjpqzedflywv79bjk2ouss29t8
- vertexaisearch.cloud.google.com — Auziyqg Ewtbwxkfdjtgsbprpy9eimbqzlleprqdyiwuj0h6g80xsyljgotkqkps7nbzwi63exkyy3maa86 K4vw2k6jfue Zjeq02lia03jznd9wo35oxkt7pzldemsbqkiroogur7mdkul Hko Lonrht Bgt0q98g 91aknxvdp8jaq==
- vertexaisearch.cloud.google.com — Auziyqgvl4oeygjbmsqe54bwty9klylwqwnsbsd 7zix8goehccoipp5t9fhez43tni1iih 18381o3jzrxukb0jg6ucfvcz Bexcfx0cqpomlwexwfwszkwsokff2ke Qgslnktjmczrqdp5obbui5onfv380m6aziq2ls9ip0paedokx Csqgxw==
- vertexaisearch.cloud.google.com — Auziyqf6c9bbd8iou2jcx9mfuwje38 9hkdtmblmvsc1ilvydzel1xvkm0nr5gjpallxfrie Vg9m84a Qt06 Oypind4vu Pprbslwnyjvtd5z9vgrdzqv27 Vc5oz6x Xe059bqtgexdfywhx45sqzfc Crgw4uxp519x0bmpwtww15cybuttpbq Jurmxi5xhupa5hmdcssgp6rqsq7j7kivw9z8=
- vertexaisearch.cloud.google.com — Auziyqfse05kbsekfzaeyejz 4khv Hfncfnmzhm9hq0eyac8wn Qiov0bbqbaa6asbnlfrjfjf8p7rfwmrqles1gs Q2j4vui0udikxfapj7m5iy 2hkkxhstvnhmls Gotuqxjnufuffdffvo=
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: AWS Machine Learning Blog ↗