Spyware Vendors, China Hackers Led 2025 Zero-Days
💡Record 2025 zero-days hit enterprise tech—secure your AI infra now
⚡ 30-Second TL;DR
What Changed
2025 zero-day exploits reached all-time high per Google TAG.
Why It Matters
Heightened zero-day risks demand stronger enterprise security for AI deployments. AI infrastructure like cloud APIs and models face elevated threats from state-sponsored actors.
What To Do Next
Audit your enterprise AI stack for the 43 reported zero-days using Google's TAG vulnerability list.
🧠 Deep Insight
Web-grounded analysis with 10 cited sources.
🔑 Enhanced Key Takeaways
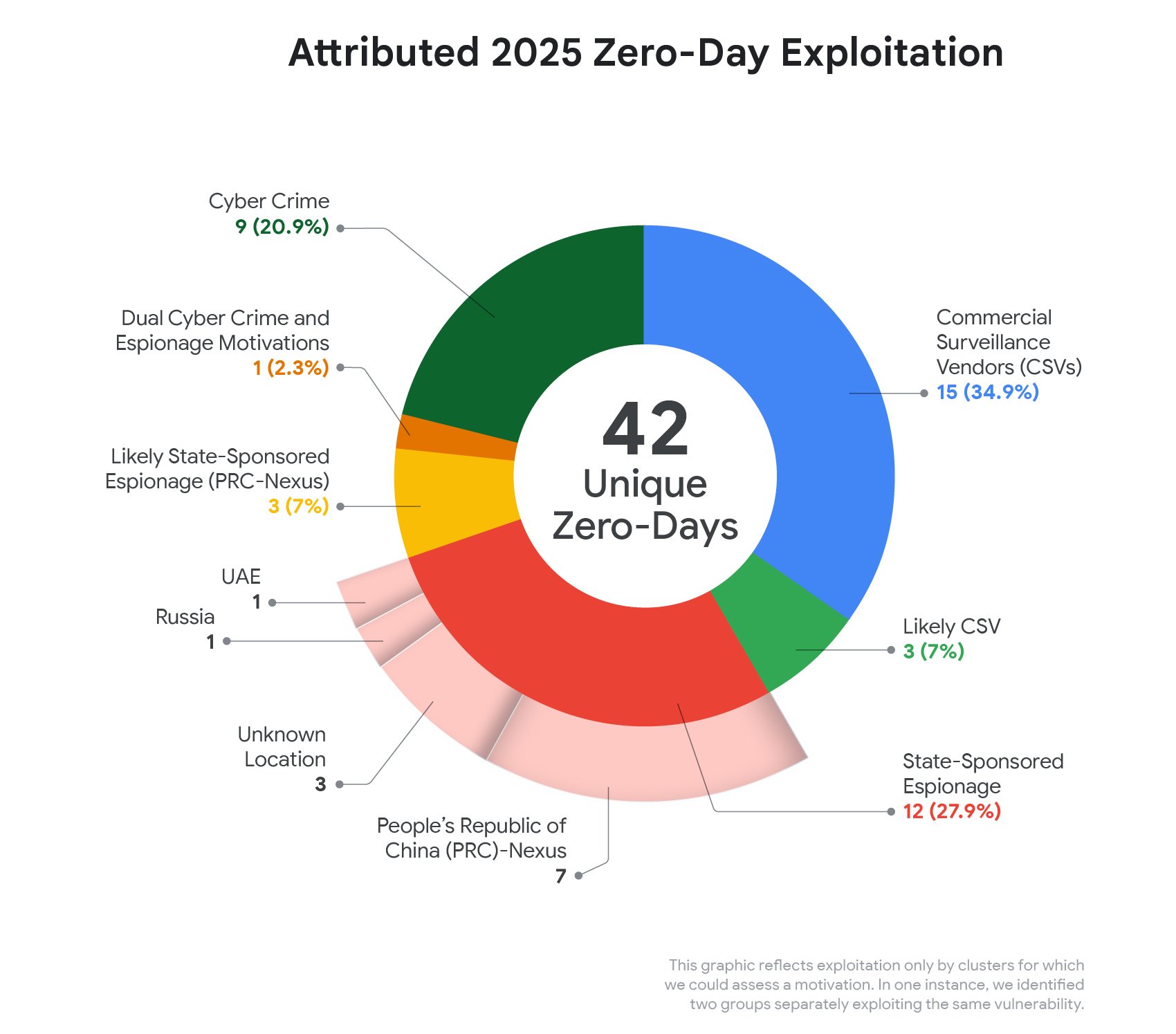
- •Commercial surveillance vendors were attributed to 15 of 42 tracked zero-days, surpassing state-sponsored groups (12) for the first time[1][2].
- •China-nexus espionage groups exploited at least 10 zero-days, doubling from 2024, with UNC3886 targeting Juniper MX routers via CVE-2025-21590[2].
- •Operating systems saw 39 zero-day exploits (most common category), mobile OS 15, while browsers dropped below 10% due to improved hardening[3].
- •Google patched 8 zero-days in Chrome, including V8 type confusion flaws CVE-2025-10585 and CVE-2025-13223 linked to spyware vendors[5].
🛠️ Technical Deep Dive
- •CVE-2025-10585: Type confusion in Chrome V8 JavaScript engine's JIT optimization pipeline, enabling heap corruption via crafted HTML; patched in 24 hours after GTIG discovery[5].
- •CVE-2025-13223: V8 vulnerability exploited in espionage by spyware vendors selling chains to governments; seventh Chrome zero-day of 2025[5].
- •Operation ForumTroll chain: Undisclosed renderer exploit + CVE-2025-2783 sandbox escape deploying Trinper backdoor; prompted Firefox CVE-2025-2857 patch[5].
- •SonicWall attacks: Chained authentication bypass, RCE, and privilege escalation vulnerabilities targeting enterprise appliances[3].
- •CVE-2025-21590: Improper isolation in Juniper MX routers exploited by UNC3886 for network access[2].
🔮 Future ImplicationsAI analysis grounded in cited sources
⏳ Timeline
📎 Sources (10)
Factual claims are grounded in the sources below. Forward-looking analysis is AI-generated interpretation.
- cloud.google.com — 2025 Zero Day Review
- cybersecuritydive.com — 814021
- securityaffairs.com — Google Gtig 90 Zero Day Flaws Exploited in 2025 As Enterprise Targets Grow
- TechCrunch — Google Says Half of All Zero Days It Tracked in 2025 Targeted Buggy Enterprise Tech
- bromium.com — Reviewing Zero Day Vulnerabilities Exploited in Malware Campaigns in 2025
- securityboulevard.com — Spyware Makers in 2025 for the First Time Topped Googles Lists of Zero Day Exploits
- therecord.media — Google Says 90 Zero Days Exploited Apt Spyware Vendors
- projectzero.google
- cloud.google.com — Coruna Powerful Ios Exploit Kit
- securityweek.com — Google Half of 2025s 90 Exploited Zero Days Aimed at Enterprises
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: cnBeta (Full RSS) ↗


