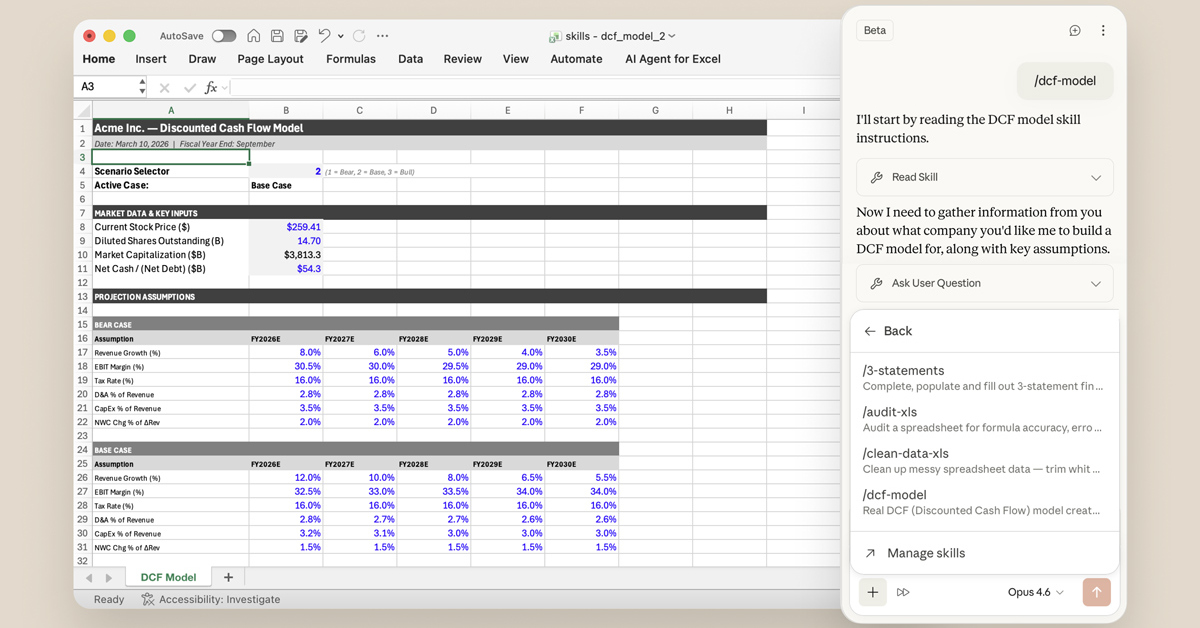
Claude Cowork Audits Chrome Extensions

💡AI agent Claude Cowork audits Chrome extensions—new security workflow for devs.
⚡ 30-Second TL;DR
What Changed
Chrome extensions offer convenience but spark safety concerns.
Why It Matters
This showcases practical AI application in cybersecurity, helping users identify risky extensions without manual effort. For AI practitioners, it highlights agentic AI potential in dev tools and personal workflows.
What To Do Next
Prompt Claude Cowork to analyze your Chrome extensions' permissions and behaviors for security risks.
🧠 Deep Insight
Web-grounded analysis with 8 cited sources.
🔑 Enhanced Key Takeaways
- •Claude Cowork lacks audit logging and compliance API integration, making it unsuitable for regulated workloads and creating accountability gaps for enterprise security teams[3].
- •Prompt injection attacks represent the primary attack vector for Claude in Chrome, with adversaries embedding hidden instructions in web content, emails, and documents that can override user commands and trigger unintended actions[2][4].
- •Claude Desktop Extensions run unsandboxed with full system privileges, enabling zero-click remote code execution attacks—rated CVSS 10/10—through chained connectors like Google Calendar, a vulnerability Anthropic has declined to fix[2][5].
🛠️ Technical Deep Dive
- •Claude's content scanning uses classifiers to detect adversarial commands embedded in hidden text, manipulated images, and deceptive UI elements within untrusted content[4].
- •The Claude in Chrome extension maintains persistent login credentials and can execute JavaScript on any visited page, creating an always-on attack surface that never shrinks[2].
- •Cowork activity is excluded from audit logs, Compliance API, and data exports, preventing forensic analysis and compliance monitoring[3].
- •Claude Cowork inherits access to the entire browser session, including all logged-in accounts, personal email, AWS credentials, and internal tools visible in the active tab[6].
- •Anthropic's Opus 4.5 model achieves a 1% attack success rate against prompt injection attempts, though security researchers question the acceptability of this failure rate for critical tasks[2].
🔮 Future ImplicationsAI analysis grounded in cited sources
⏳ Timeline
📎 Sources (8)
Factual claims are grounded in the sources below. Forward-looking analysis is AI-generated interpretation.
- tactiq.io — How to Use Claude Cowork Chrome Extension
- wonderingaboutai.substack.com — Is Claude Cowork Safe
- support.claude.com — 13364135 Use Cowork Safely
- almcorp.com — Claude for Chrome Complete Guide
- techradar.com — Claude Desktop Extension Can Be Hijacked to Send Out Malware by a Simple Google Calendar Event
- harmonic.security — Security Lessons From Claude Codes First Year
- Anthropic — Claude Code Security
- wavespeed.ai — Claude Cowork 2026 AI Game Changer
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: ITmedia AI+ (日本) ↗