Chrome Extension Hijacked, 1M+ Users Hit by Malware
💡Image tool hijack threatens ML workflows using Chrome extensions
⚡ 30-Second TL;DR
What Changed
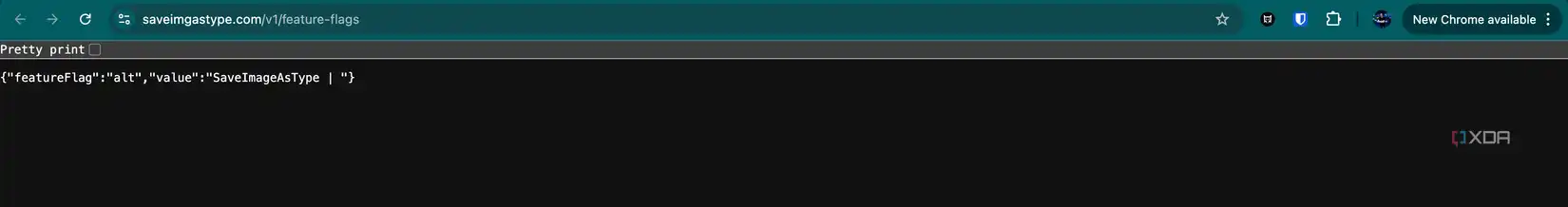
Save Image as Type Chrome extension hijacked by hackers
Why It Matters
Exposes supply chain risks in browser extensions, urging users to audit tools used in development workflows. Could affect image processing pipelines in AI projects.
What To Do Next
Audit Chrome extensions via chrome://extensions/ and uninstall Save Image as Type immediately.
🧠 Deep Insight
Web-grounded analysis with 6 cited sources.
🔑 Enhanced Key Takeaways
- •The malware in 'Save image as Type' injected affiliate links from 578 identifiable sites into users' clicks, stealing commissions from purchases.[3]
- •Extension ownership changed in late 2025 from Image4Tools to 'Lauren Bridge', likely indicating a sale that preceded the malicious activity.[3]
- •Microsoft removed the Edge version of the extension in February 2025 after detecting malware, over a year before Google's action.[1][3][5]
🛠️ Technical Deep Dive
🔮 Future ImplicationsAI analysis grounded in cited sources
⏳ Timeline
📎 Sources (6)
Factual claims are grounded in the sources below. Forward-looking analysis is AI-generated interpretation.
- windowscentral.com — Google Promoted a Malicious Chrome Extension After Microsoft Banned It
- androidauthority.com — Favorite Chrome Image Extension Malware 3649252
- 9to5google.com — Image Saving Chrome Extension Removed As Malware
- support.google.com — Chrome Disabled Save Image As Type Extension for Malware %e2%80%93 False Positive or Real Threat
- xda-developers.com — Google Featuring Chrome Extension Months Malicious
- androidpolice.com — This Popular Image Saving Chrome Extension Was Stealing Your Data
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: cnBeta (Full RSS) ↗


