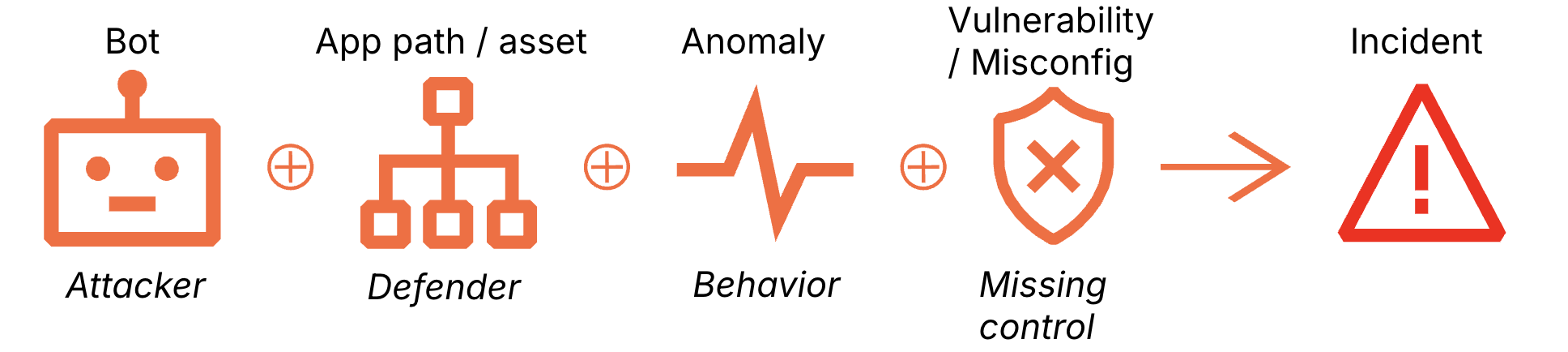
Toxic Combinations Spark Security Incidents
💡Catch hidden breaches from tiny signals—key for secure AI web apps
⚡ 30-Second TL;DR
What Changed
Minor misconfigurations appear harmless in isolation
Why It Matters
Highlights need for correlated signal monitoring in cloud security. Helps prevent escalation of subtle issues into breaches. Crucial for maintaining robust web application defenses.
What To Do Next
Review Cloudflare dashboard logs for correlating minor anomalies today.
🧠 Deep Insight
Web-grounded analysis with 8 cited sources.
🔑 Enhanced Key Takeaways
- •Toxic combinations represent a paradigm shift in threat detection: rather than evaluating individual requests in isolation, security systems must analyze the confluence of multiple signals across behavioral patterns, bot activity, and application-layer vulnerabilities to identify brewing incidents[1].
- •Real-world toxic combination attacks have targeted high-value assets through chained exploitation: the Midnight Blizzard attack leveraged compromised OAuth tokens from a prior Okta breach combined with legacy accounts lacking MFA to escalate privileges and exfiltrate senior staff emails[3][4].
- •Multi-cloud environments create blind spots that amplify toxic combination risks: siloed accounts and data sprawl across cloud providers make it difficult to discover converging misconfigurations, overly permissive identities, and leaked secrets that collectively enable compromise[6].
- •Toxic combinations in cloud security extend beyond traditional web application attacks to include AI-driven behaviors: enterprises now face converging risks from permissions, settings, and AI agent actions that collectively create breach pathways[7].
- •Detection requires behavioral context analysis rather than point defenses: Web Application Firewalls, bot detection, and API protection tools that focus on individual request risk miss the broader intent signals that emerge when multiple minor anomalies converge[1].
🛠️ Technical Deep Dive
- •Toxic combination detection ingredients identified by Cloudflare include: Bot Score < 30 (high probability of automated traffic with exploit script signatures), HTTP 200 on sensitive paths (successful responses from login endpoints that should trigger WAF blocks), Repeated Mutations (high-frequency payload variations indicating attacker tuning), and Suspicious Query Patterns (SLEEP commands and time-based database probing)[1].
- •Mitigation strategies for toxic combinations include: deploying geo-blocking to restrict administrative access to specific countries, enforcing multi-factor authentication on every administrative entry point, and monitoring for repeated mutations and anomalous query patterns that indicate payload tuning[1].
- •Attack chain analysis from the Cloudflare-Atlassian incident reveals a six-step privilege escalation: (1) password spray on legacy accounts without MFA, (2) hijacking legacy OAuth apps with high-level permissions, (3) creating malicious OAuth apps, (4) granting admin Exchange permissions, (5) escalating privileges to a new controlled user, (6) granting full M365 Exchange Online access[3][4].
- •Risk scoring in multi-cloud environments dynamically incorporates: number of attack paths associated with alerts, asset context (running vs. marked for deletion), exposure information (public accessibility), sensitive data at risk, and standard CVSS/EPSS scores[6].
🔮 Future ImplicationsAI analysis grounded in cited sources
⏳ Timeline
📎 Sources (8)
Factual claims are grounded in the sources below. Forward-looking analysis is AI-generated interpretation.
- blog.cloudflare.com — Toxic Combinations Security
- scouts.yutori.com — Bb4f3fe7 B4d2 4043 9a34 4319f19190fa
- appomni.com — Midnight Blizzard and Cloudflare Atlassian Cybersecurity Incidents
- thehackernews.com — Midnight Blizzard and Cloudflare
- tldrsec.com — Tldr Sec 204
- orca.security — Multi Cloud Security Federal Agencies
- cyberdefensemagazine.com — AI Agents Are Quietly Building the Next Global Breach Network Are You Ready
- approov.io — The Security Risks of Mobile Apps and Apis in the Smart Home
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: Cloudflare Blog ↗
