⚛️Ars Technica•Stalecollected in 26m
TotalRecall Tool Breaches Recall Database
💡Security flaw in Windows AI Recall exposes dev screen history to easy tools
⚡ 30-Second TL;DR
What Changed
TotalRecall Reloaded exploits delivery truck vulnerability in Recall
Why It Matters
Highlights privacy risks in on-device AI features storing user activity data. Microsoft users, especially developers, should review Recall security. May prompt patches affecting AI workflow tools on Windows.
What To Do Next
Download TotalRecall Reloaded to test and secure your Windows Recall database exposure.
Who should care:Enterprise & Security Teams
🧠 Deep Insight
AI-generated analysis for this event.
🔑 Enhanced Key Takeaways
- •The TotalRecall tool specifically targets the unencrypted SQLite database files generated by the Windows Recall feature, which are stored in the user's local AppData directory.
- •Security researchers identified that while the 'vault' (the encrypted storage layer) is robust, the tool leverages a lack of proper access control lists (ACLs) on the temporary staging folders where snapshots are processed before encryption.
- •Microsoft has acknowledged the vulnerability, noting that the issue stems from the 'delivery mechanism'—specifically, the process that moves raw screen data from the capture service to the encrypted database—rather than a flaw in the encryption algorithm itself.
🛠️ Technical Deep Dive
- •The vulnerability exploits the 'Recall Data Staging' directory, which temporarily holds raw .png or .bmp snapshots before they are processed by the Windows AI engine.
- •TotalRecall Reloaded utilizes a file-system watcher to intercept these files during the brief window between capture and vault ingestion.
- •The tool bypasses the need for decryption keys by accessing the data in its pre-encrypted state, effectively performing a 'man-in-the-middle' attack on the local file system.
- •The exploit relies on the fact that the staging directory inherits the permissions of the user profile, allowing any process running with user-level privileges to read the files.
🔮 Future ImplicationsAI analysis grounded in cited sources
Microsoft will mandate hardware-backed encryption for all Recall staging directories in the next Windows 11 update.
The current vulnerability highlights a critical gap in the data pipeline that can only be closed by ensuring data is encrypted at the point of capture.
Third-party security vendors will release 'Recall-aware' endpoint detection and response (EDR) modules by Q3 2026.
The high-profile nature of this breach necessitates specialized monitoring tools to detect unauthorized access to the Recall staging path.
⏳ Timeline
2024-05
Microsoft officially announces Windows Recall as a flagship AI feature for Copilot+ PCs.
2024-06
Microsoft delays the public release of Recall following widespread security and privacy concerns from researchers.
2024-10
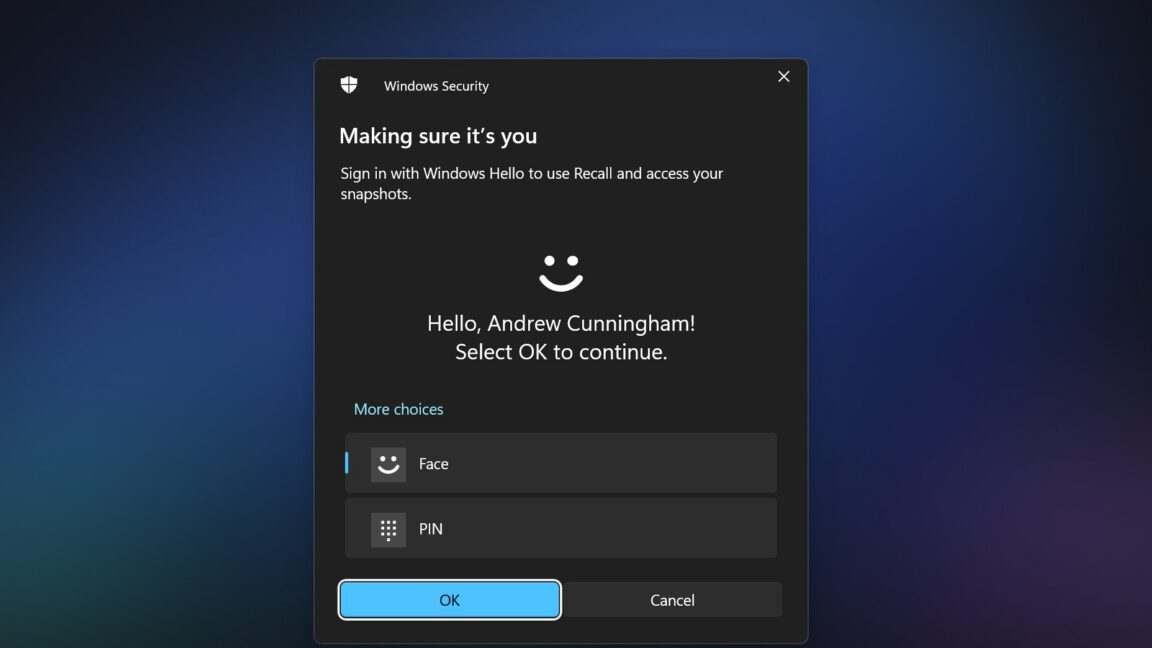
Microsoft re-releases Recall to Windows Insiders with enhanced security measures, including mandatory Windows Hello authentication.
2026-04
TotalRecall Reloaded tool is released, exposing the vulnerability in the Recall delivery mechanism.
📰 Event Coverage
📰
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: Ars Technica ↗