🇨🇳cnBeta (Full RSS)•Recentcollected in 51m
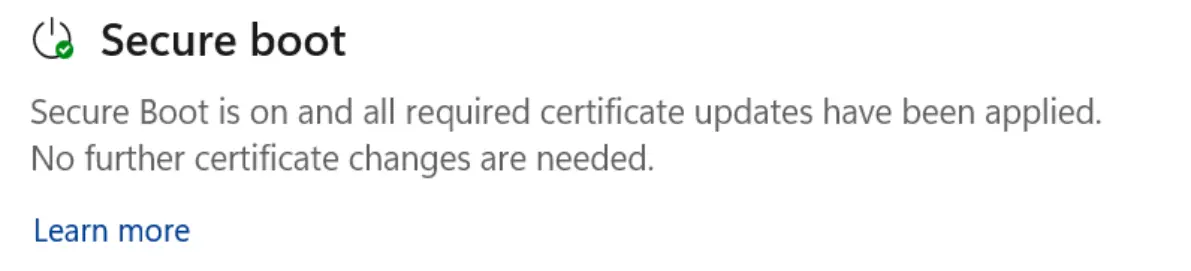
Microsoft Adds Color Secure Boot Alerts
💡Secure Boot expiry alerts safeguard Windows for local AI model runs and deployments.
⚡ 30-Second TL;DR
What Changed
Secure Boot certificates expiring in June 2024
Why It Matters
Boosts security hygiene for Windows users, reducing risks from expired certs in AI dev and enterprise setups.
What To Do Next
Launch Windows Security Center on your machines to inspect the new Secure Boot color status.
Who should care:Enterprise & Security Teams
🧠 Deep Insight
AI-generated analysis for this event.
🔑 Enhanced Key Takeaways
- •The Secure Boot certificate expiration specifically concerns the 'Microsoft Corporation UEFI CA 2011' certificate, which is a critical component for verifying bootloader integrity on Windows devices.
- •The color-coded alert system is integrated into the Windows Security Center to address the 'BlackLotus' UEFI bootkit threat, which exploits vulnerabilities in older, signed bootloaders.
- •Microsoft has provided specific PowerShell scripts and WMI (Windows Management Instrumentation) queries alongside the UI updates to allow enterprise administrators to audit certificate status across large fleets remotely.
🛠️ Technical Deep Dive
- •The feature monitors the status of the UEFI Secure Boot Forbidden Signature Database (dbx) and the presence of valid Microsoft-signed UEFI CA certificates.
- •The UI indicators are driven by the Windows Health Attestation service, which evaluates the device's boot chain against known-good signatures stored in the firmware's NVRAM.
- •The system utilizes the 'Get-SecureBootUEFI' PowerShell cmdlet to retrieve the current state of the UEFI variables, which the Security Center then maps to the color-coded status (Green: Secure/Updated, Yellow: Warning/Action Required, Red: Critical/Vulnerable).
🔮 Future ImplicationsAI analysis grounded in cited sources
Increased adoption of automated UEFI firmware update policies in enterprise environments.
The visibility provided by the new alerts will force IT departments to prioritize firmware patching to avoid 'Red' status indicators in their security dashboards.
Shift toward hardware-backed security attestation for Windows compliance.
By surfacing low-level boot status in the user-facing Security Center, Microsoft is conditioning users and admins to treat firmware integrity as a primary metric for device health.
⏳ Timeline
2011-01
Microsoft Corporation UEFI CA 2011 certificate is issued for bootloader signing.
2022-10
Microsoft releases security updates to address BlackLotus UEFI bootkit vulnerabilities.
2024-06
Initial expiration window for the 2011 UEFI CA certificate begins.
2026-04
Microsoft rolls out color-coded Secure Boot alerts in Windows Security Center.
📰
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: cnBeta (Full RSS) ↗