🗾ITmedia AI+ (日本)•Stalecollected in 2h
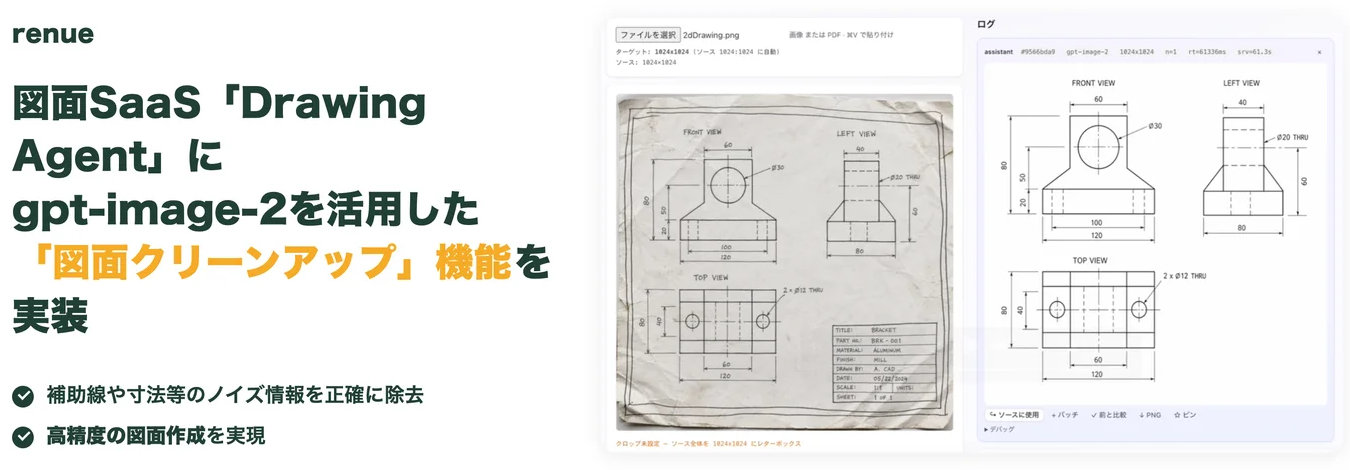
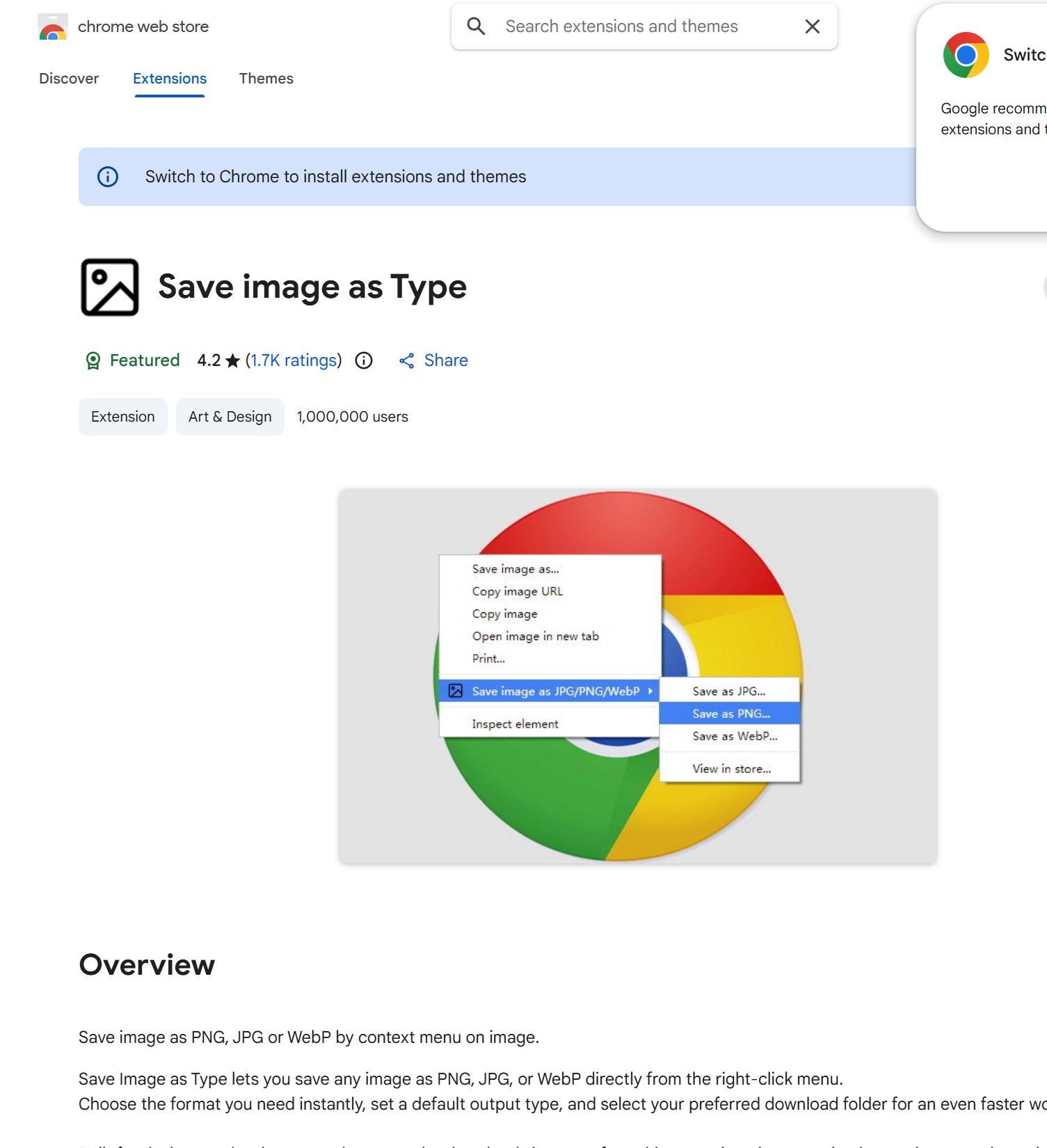
Image Saver Extension Axed for Malware; AI Recreates It
💡Users rebuild malware-killed extension with AI—fast prototyping trend for devs
⚡ 30-Second TL;DR
What Changed
Chrome extension removed after malware detection
Why It Matters
Highlights rising reliance on AI for rapid prototyping amid tool disruptions, accelerating no-code dev for extensions.
What To Do Next
Prompt an AI code generator like Cursor to build a malware-free image format converter Chrome extension.
Who should care:Developers & AI Engineers
🧠 Deep Insight
AI-generated analysis for this event.
🔑 Enhanced Key Takeaways
- •The malware identified in the extension was a sophisticated 'man-in-the-middle' script designed to inject unauthorized affiliate links into e-commerce sites visited by users.
- •Google's automated Web Store security scanners flagged the extension after a sudden update pushed by a third-party developer who had purchased the extension from the original creator.
- •The surge in AI-generated replacements is being driven by LLMs like Claude 3.7 and GPT-5, which can generate the manifest.json and background.js files required for a functional Chrome extension in seconds.
🛠️ Technical Deep Dive
- •The malicious payload utilized a 'content script' injection technique to monitor DOM changes on target domains.
- •The AI-generated replacements typically utilize the 'chrome.downloads' API to bypass standard browser 'save as' dialogs, allowing for batch processing of image assets.
- •Most user-created replacements are being distributed as 'unpacked' extensions, requiring users to enable 'Developer Mode' in Chrome to bypass the Web Store's current vetting process.
🔮 Future ImplicationsAI analysis grounded in cited sources
Google will implement mandatory code-signing for all Chrome extension updates.
The prevalence of 'account hijacking' where malicious actors buy legitimate extensions necessitates a more rigorous identity verification process for developers.
The 'unpacked' extension market will see a 40% increase in security vulnerabilities.
As users turn to AI to generate their own tools, they lack the security expertise to audit the generated code for hidden vulnerabilities or malicious dependencies.
⏳ Timeline
2024-11
Original extension reaches 500,000 active users.
2026-01
Original developer sells the extension to an undisclosed third-party entity.
2026-03-15
Malicious update is pushed to the Chrome Web Store.
2026-03-22
Google removes the extension following reports of unauthorized affiliate link injection.
📰
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: ITmedia AI+ (日本) ↗