🇨🇳cnBeta (Full RSS)•Stalecollected in 5m
Google Accelerates Quantum-Safe Crypto to 2029
💡Google's early quantum security push warns AI devs of urgent infra hardening needs.
⚡ 30-Second TL;DR
What Changed
Complete infrastructure migration to post-quantum cryptography by 2029
Why It Matters
Accelerates industry shift to PQC, forcing AI firms to prioritize quantum-resistant security for data and models sooner. Enhances Google's leadership in secure cloud infrastructure critical for AI workloads.
What To Do Next
Audit your encryption stacks against NIST PQC finalists like Kyber and Dilithium.
Who should care:Enterprise & Security Teams
🧠 Deep Insight
AI-generated analysis for this event.
🔑 Enhanced Key Takeaways
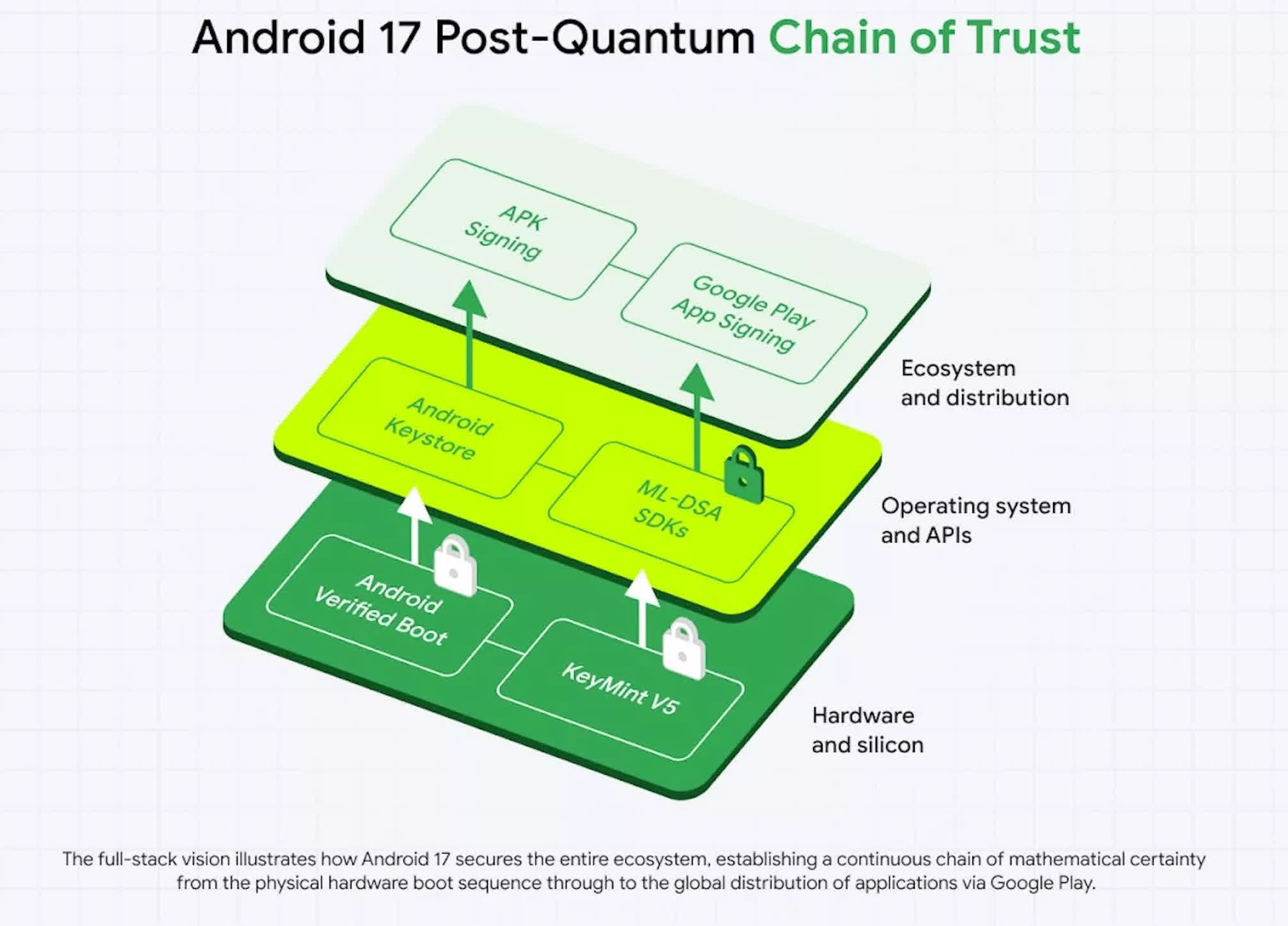
- •Google's 2029 target aligns with the NIST finalized standards for post-quantum algorithms (ML-KEM, ML-DSA, and SLH-DSA) released in August 2024, which form the backbone of their migration strategy.
- •The migration effort leverages Google's 'hybrid' encryption approach, which combines classical algorithms (like X25519) with quantum-resistant ones to ensure security even if a new PQC algorithm is found to have vulnerabilities.
- •Internal research indicates that Google is prioritizing the protection of 'harvest now, decrypt later' data, specifically targeting long-lived cloud storage and identity tokens that remain sensitive beyond the projected Q-Day window.
📊 Competitor Analysis▸ Show
| Feature | Google (PQC Migration) | Microsoft (PQC Migration) | AWS (PQC Migration) |
|---|---|---|---|
| Primary Strategy | Hybrid (Classical + PQC) | Hybrid (Classical + PQC) | Hybrid (Classical + PQC) |
| Public Deadline | 2029 | Not explicitly stated | Not explicitly stated |
| NIST Compliance | Full (ML-KEM/DSA) | Full (ML-KEM/DSA) | Full (ML-KEM/DSA) |
🛠️ Technical Deep Dive
- •Implementation of FIPS 203 (ML-KEM) for key encapsulation mechanisms to replace RSA and Elliptic Curve Diffie-Hellman.
- •Deployment of FIPS 204 (ML-DSA) for digital signatures to secure TLS handshakes and software update verification.
- •Utilization of 'Hybrid Key Exchange' in Chrome and Google Cloud services, requiring both a classical ECDH share and a Kyber/ML-KEM share to establish a session key.
- •Integration of PQC-ready libraries into BoringSSL to facilitate rapid deployment across Google's global infrastructure.
🔮 Future ImplicationsAI analysis grounded in cited sources
Hardware security modules (HSMs) will require mandatory firmware updates by 2027.
Existing HSMs lack the computational overhead capacity to handle the larger key sizes and signature lengths required by NIST-standardized PQC algorithms.
Cloud service providers will experience a 10-15% increase in latency for initial TLS handshakes.
The increased size of PQC public keys and signatures results in more network round-trips and higher processing requirements compared to classical ECC.
⏳ Timeline
2023-08
Google Chrome begins testing Kyber-768 in TLS 1.3 handshakes.
2024-08
NIST officially releases the first three finalized post-quantum cryptography standards.
2025-02
Google announces the expansion of PQC support across Google Cloud's load balancing infrastructure.
📰
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: cnBeta (Full RSS) ↗