☁️AWS Machine Learning Blog•Stalecollected in 2m
AWS Firewall Restricts AI Agent Domains
💡Secure AI agents from rogue domains using AWS Firewall SNI—vital for safe production deploys.
⚡ 30-Second TL;DR
What Changed
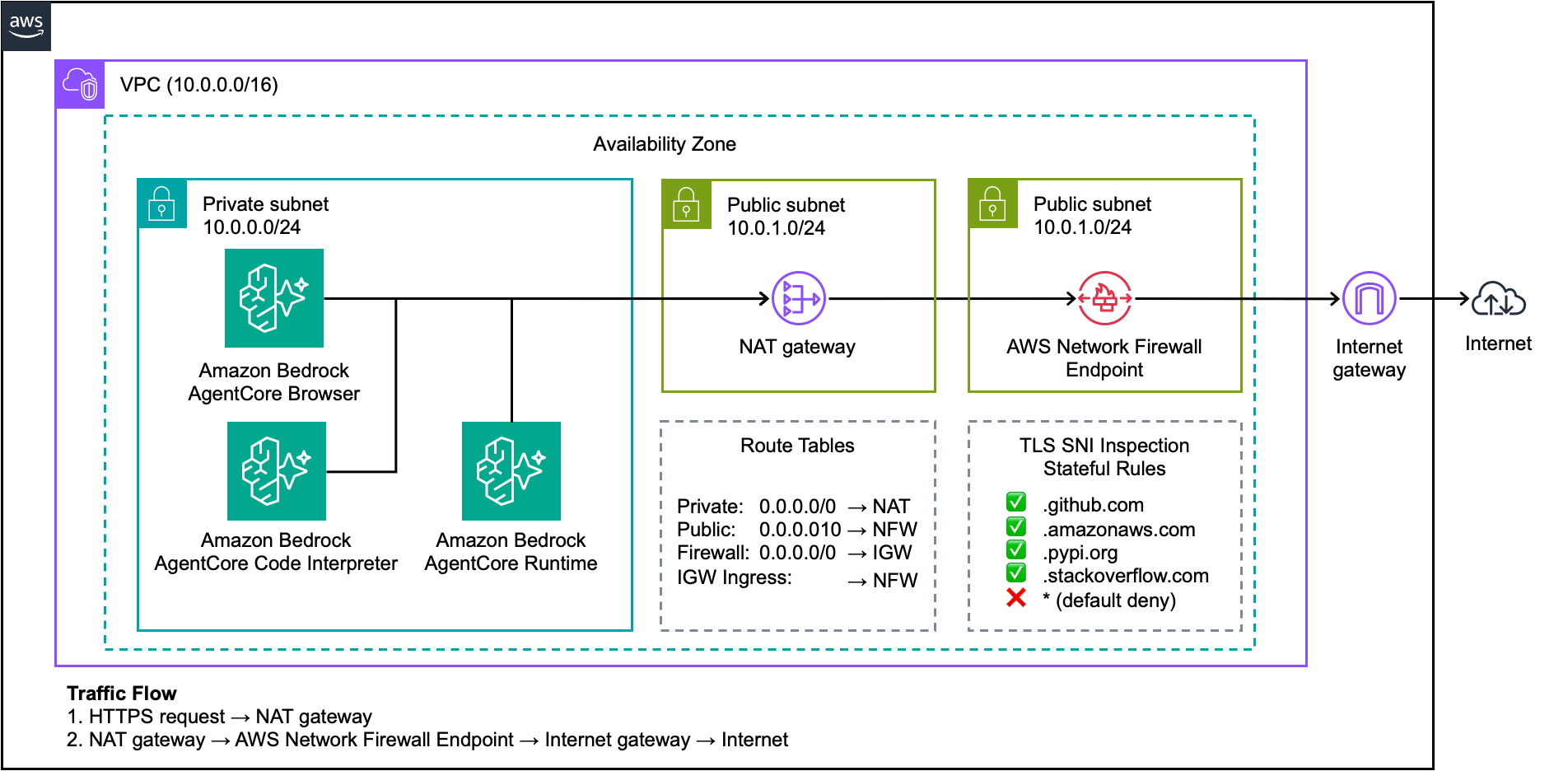
Configure AWS Network Firewall for domain allowlisting
Why It Matters
This update bolsters AI agent security by preventing unauthorized domain access, crucial for enterprise compliance and risk reduction. AI practitioners can deploy agents more confidently in production environments.
What To Do Next
Configure an AWS Network Firewall policy with SNI domain allowlist for AgentCore AI agents.
Who should care:Enterprise & Security Teams
🧠 Deep Insight
AI-generated analysis for this event.
🔑 Enhanced Key Takeaways
- •The implementation leverages AWS Network Firewall's stateful rule groups specifically configured for TLS inspection, which is required to extract the SNI field from encrypted traffic.
- •This architecture addresses the 'agent exfiltration' risk, where autonomous agents might be prompted to send sensitive data to unauthorized third-party command-and-control (C2) servers.
- •AWS provides pre-built Managed Rule Groups for AI/ML services, allowing users to combine domain allowlisting with threat intelligence feeds to block known malicious AI-related infrastructure.
📊 Competitor Analysis▸ Show
| Feature | AWS Network Firewall (AgentCore) | Google Cloud Firewall Plus | Azure Firewall Premium |
|---|---|---|---|
| SNI Filtering | Native via TLS Inspection | Native via FQDN Filtering | Native via FQDN Filtering |
| AI Agent Integration | Deep integration with AgentCore | Integration with Vertex AI Agents | Integration with Azure AI Agents |
| Pricing Model | Hourly + Data Processing | Hourly + Data Processing | Hourly + Data Processing |
| Threat Intelligence | AWS Managed Rules | Google Cloud Threat Intelligence | Microsoft Cyber Security Intelligence |
🛠️ Technical Deep Dive
- •Requires the deployment of an AWS Network Firewall endpoint within a dedicated inspection VPC.
- •Traffic must be routed through the firewall using VPC route table modifications (Gateway Load Balancer endpoints).
- •TLS inspection requires the installation of a CA certificate on the client instances (or the agent host) to perform man-in-the-middle decryption for SNI verification.
- •Rules are defined using the Suricata-compatible rule format, specifically utilizing the 'tls.sni' keyword for domain matching.
- •Supports integration with AWS Resource Access Manager (RAM) for centralized management of firewall policies across multiple accounts.
🔮 Future ImplicationsAI analysis grounded in cited sources
Automated policy generation for AI agents will become standard.
Manual domain allowlisting is not scalable for complex agent workflows, necessitating AI-driven tools that automatically discover and whitelist required domains.
Agent-level identity will supersede IP-based firewall rules.
As agents become more mobile and ephemeral, security policies will shift toward verifying the cryptographic identity of the agent rather than the network path it traverses.
⏳ Timeline
2023-11
AWS introduces AgentCore framework for enterprise AI agent development.
2024-05
AWS Network Firewall adds enhanced TLS inspection capabilities for granular traffic control.
2025-09
AWS releases initial security best practices for securing generative AI agent deployments.
📰
Weekly AI Recap
Read this week's curated digest of top AI events →
👉Related Updates
AI-curated news aggregator. All content rights belong to original publishers.
Original source: AWS Machine Learning Blog ↗